what to do with an encrypted cache key
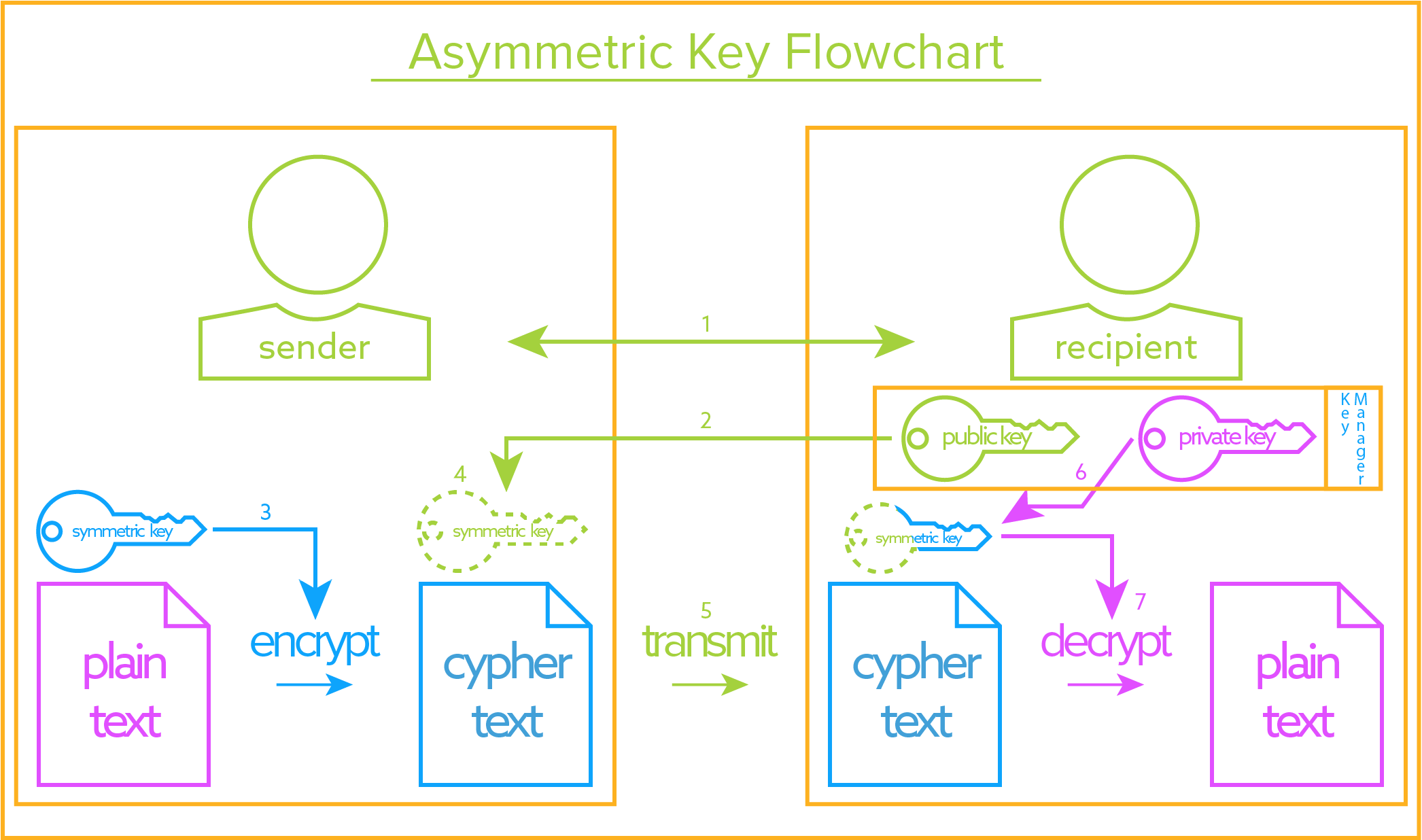
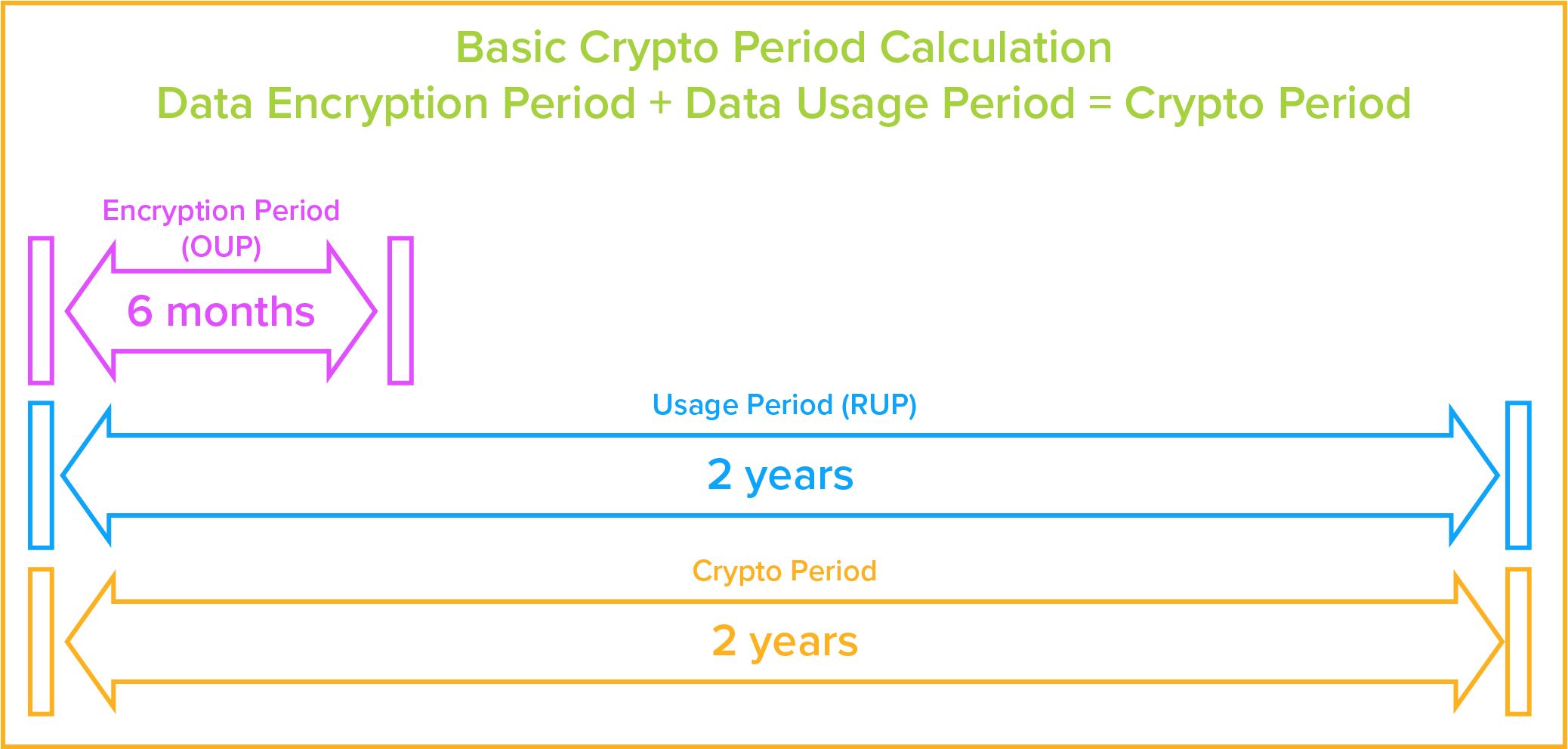
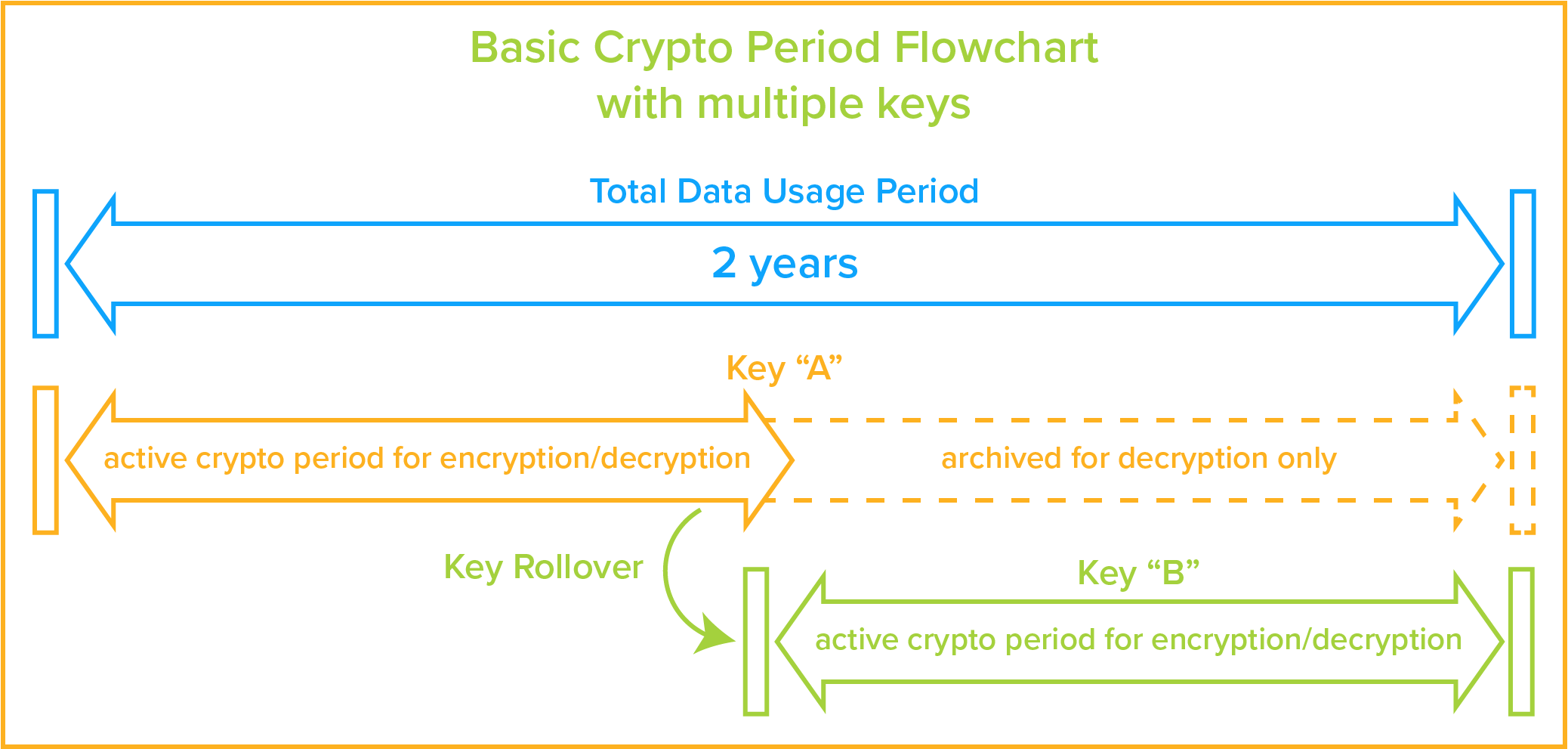
Encryption key direction is administering the full lifecycle of cryptographic keys. This includes: generating, using, storing, archiving, and deleting of keys. Protection of the encryption keys includes limiting access to the keys physically, logically, and through user/role access. ^Dorsum to Top Permit'southward get started with a brief overview of the types of encryption keys. ^Back to Summit In symmetric fundamental cryptography, the aforementioned encryption key is used to both encrypt and decrypt the data. This means of encryption is used primarily to protect data at rest. An case would exist to encrypt sensitive data into ciphertext while it is stored in a database and decrypt it to plaintext when it is accessed by an authorized user, and vice versa. Asymmetric keys, on the other hand, are a pair of keys for the encryption and decryption of the data. Both keys are related to each other and created at the same fourth dimension. They are referred to equally a public and a private key: ^Back to Top First, let's found a few definitions: Now that we accept the definitions in identify, below is a step by step example of how an authorized user accesses encrypted data: ^Back to Elevation The encryption key life-bike, divers by NIST as having a pre-operational, operational, post-operational, and deletion stages, requires that, amongst other things, a operational crypto flow exist defined for each cardinal. A crypto period is the "time bridge during which a specific primal is authorized for use" and in Section 5.3 of NIST's Guide, the crypto catamenia is adamant (for example, with a symmetric primal) by combining the estimated fourth dimension during which encryption volition be applied to data (the Originator Usage Menses (OUP)) and the fourth dimension when information technology will exist decrypted for employ (the Recipient Usage Period (RUP)). So, as an example: Merely, since an organisation may reasonably want to encrypt and decrypt the same data for years on end, other factors may come up into play to when factoring the crypto period: You may want to limit the: This can exist boiled down to a few key questions: The general rule: as the sensitivity of data being secured increases, the lifetime of an encryption key decreases. Given this, your encryption key may have an active life shorter than an authorized user's admission to the information. This means that you will need to archive de-activated keys and utilize them only for decryption. Once the data has been decrypted by the old primal, it will be encrypted past the new key, and over time the old fundamental will no longer be usedto encrypt/decrypt data and tin can be deleted. (see graphic beneath) Run into below for a more thorough understanding of a keys total life-cycle. The encryption key is created and stored on the key management server. The key director creates the encryption key through the use of a cryptographically secure random fleck generator and stores the key, along with all it'southward attributes, into the key storage database. The attributes stored with the key include its proper noun, activation engagement, size, instance, the ability for the cardinal to be deleted, as well as its rollover, mirroring, key access, and other attributes. The key tin be activated upon its creation or set up to be activated automatically or manually at a later time. The encryption key manager should track electric current and past instances (or versions) of the encryption key. You need to be able to choose whether or not the cardinal tin can exist deleted, mirrored to a failover unit, and past which users or groups information technology can exist accessed. Your key manager should permit the administrator to change many of the key'south attributes at any time. An ambassador should exist able to use the key manager to revoke a cardinal so that it is no longer used for encryption and decryption requests. A revoked primal tin, if needed, be reactivated by an administrator so that, In sure cases the central can be used to decrypt data previously encrypted with it, like old backups. But even that tin can be restricted. NIST (Section eight.3.1) requires that an annal should exist kept for deactivated keys. The archive should "protect the archived fabric from unauthorized [disclosure,] modification, deletion, and insertion." The encryption keys need "to be recoverable … subsequently the end of its cryptoperiod" and "the system shall exist designed to allow reconstruction" of the keys should they need to be reactivated for employ in decrypting the data that information technology once encrypted. If a cardinal is no longer in utilise or if information technology has somehow been compromised, an administrator tin can cull to delete the key entirely from the primal storage database of the encryption central manager. The key director will remove it and all its instances, or simply certain instances, completely and make the recovery of that fundamental impossible (other than through a restore from a backup image). This should be available every bit an option if sensitive data is compromised in its encrypted country. If the key is deleted, the compromised data will be completely secure and unrecoverable since it would be incommunicable to recreate the encryption fundamental for that data. ^Back to Top In "Recommendation for Central Management – Part two" NIST defines Separation of Duties equally: The practice of Separation of Duties reduces the potential for fraud or malfeasance by dividing related responsibilities for critical tasks between different individuals in an arrangement. It is common in the financial and accounting procedures of nigh organizations. For example, the person who prints the checks at a company would not be the person who signs the checks. Similarly, the individual who signs checks would non reconcile the depository financial institution statements. A company would ensure that business disquisitional duties are categorized into four types of functions: say-so, custody, tape keeping, and reconciliation. In a perfect system, no i person should handle more than than ane type of part. Regarding information security practices, the implementation of Separation of Duties is critical in the area of encryption key management. To prevent unwanted access to protected data, it is important that the person who manages encryption keys not have the power to access protected data, and vice versa. This is no more difficult to accomplish in an information technology context than in a fiscal context, just is oft overlooked or misunderstood in complex computer systems. Again, NIST, in Recommendation for Key Direction – Part ii, defines Dual Control: While Separation of Duties involves distributing different parts of a process to different people, Dual Control requires that at least ii or more individuals control a unmarried process. In data security practice it is common to discover requirements for Dual Control of encryption key direction functions. Because a key management system may be storing encryption keys for multiple applications and business organisation entities, the protection of encryption keys is critically important. The concept of Split Knowledge applies to any access or treatment of unprotected cryptographic material like encryption keys or passphrases used to create encryption keys, and requires that no 1 person know the complete value of an encryption fundamental. If passphrases are used to create encryption keys, no i person should know the entire passphrase. Rather, two or more people should each know only a part of the pass phrase, and all of them would take to exist present to create or recreate an encryption fundamental. ^Back to Top Many, when talking nigh securing a key director, volition naturally turn to securing the cardinal manager itself with a hardware security module (HSM). While that is a necessary topic (and we will discuss information technology), we should outset talk about securing the physical surroundings in which your fundamental director is housed. In NIST's Special Publication 800-fourteen, they offer this definition of physical security: An organisation'due south physical security plan need to include things like: Now comes securing the cryptographic module itself. The Federal Data Processing Standards (FIPS) has identified 4 levels of increasing security in FIPS 140-2 that can exist applied to the module, each respective to the commensurate threat level: Every information security product bachelor makes claims every bit to superior functionality or information protection. But when protecting sensitive information, organizations need to have balls that a product's stated security claim is valid. This is certainly true when information technology comes to an encryption central managing director. To address this, NIST has devised a organisation to validate cryptographic modules and ensure that they comply with FIPS 140-2 standards. Here are the steps an encryption key manager vendor must to accept to prove total compliance: The adjacent arena in which you can protect your encryption keys is past logically separating the different cryptographic components housing the keys from the rest of the larger network. There are three main items to consider: Once Physical Security and Logical Security are addressed, the final component is user roles and privileges. The core concept promulgated by NIST is the concept of least privilege: where you restrict "the access privileges of authorized personnel (eastward.m., program execution privileges, file modification privileges) to the minimum necessary to perform their jobs." NIST gives guidance, in Sections v.three.5 of Recommendation for Key Direction – Part 2, on the admission controls and privileges necessary to properly manage user access to the fundamental direction system. Across limiting access to the fundamental direction server, you should as well limit access to the keys themselves based on user and group. The users and group access tin be defined on a organisation level, or at the level of each central. When yous create a key y'all can define the restrictions on user and group access. As an case: At that place is an AES encryption central bachelor on the key management server used to protect an employee'south personal data. It is restricted so that only members of the Human Resources group can use that fundamental. Then any individual with "Human Resources" defined as their individual or group role can successfully request that central, all others are turned away. Once you take concrete security, logical security, and user roles in place, you must besides consider business continuity. If an intruder does comprise your information or your product server(south) are taken offline for a diversity of reasons, y'all must be able to bounce back in a relatively brusk fourth dimension with pre-prescribed steps. Here are a couple definitions to kickoff u.s. off: Business organization Continuity: As defined by ISO 22301:2012 (Section iii.three), it is the "capability of the organization to continue delivery of products or services at adequate" levels after a "disruptive incident." Hot failover: In a network environment, a hot failover is switching to a backup server that is regularly updated from the production server and is prepare, at whatever time, should the production server no longer be able to office unremarkably for whatever length of time. In the case of key management, each product key management server should be mirrored with a high availability server in a geographically separate location in instance the product server is compromised and taken offline for whatever length of time. As an abbreviated listing, hither are some features to look for in fundamental management solutions or what yous will want to address if you build your own: ^Back to Top The hardware security module (HSM) has been discussed already in "Physical Security" mostly referred to every bit the "cryptographic module." But, to summarize, a HSM is typically a server with different levels of security protection or "hardening" that prevents tampering or loss. These can be summarized as: With many organizations moving some or all of their operations to the cloud, the need for moving their security has likewise arisen. The proficient news, many fundamental management providers have partnered with cloud hosting providers to rack upwards traditional HSMs in deject environments. The same levels of "hardening" would withal utilise, every bit it is a traditional HSM in an offsite environment. Virtual instances of an encryption primal manager offer a great deal more than flexibility than their HSM counterparts. In many cases, a virtual cardinal director can be downloaded from a vendor in a matter of minutes and deployed in a virtual environment. An HSM, on the other hand, can take days or weeks being shipped to the site and so requires a physical installation. Further, virtual instances can exist installed anywhere that supports the virtual platform that the key manager runs in, VMware, as an instance. The downside, of course, is that by information technology's nature of being virtual with no set physical components, a virtual fundamental manager'due south software tin can but be FIPS 140-2 compliant, but not validated. Then, if your business need(s) or compliance regulation(southward) require FIPS 140-two validation, then a HSM is your merely pick. That being said, the logical security that FIPS 140-two compliant virtual key managers provide is commonly more enough for most organizational needs. Deject providers, such every bit Amazon Web Services (AWS), Microsoft Azure (Azure), and more take marketplace offerings for encryption fundamental management as well as their own key direction as a service (KMaaS). AWS and Azure's KMaaS is typically multi-tenant, significant more than than 1 user's key(s) are present on the same key management example. This can raise concerns for organizations that need defended services to mitigate security concerns of other users accessing the same key data stores. To combat this result, most cloud providers will likewise offer defended services. In their marketplaces, there are also independent vendors that provide dedicated services that typically come up in 2 forms: Pay-Per-Usage and "bring your own license." Townsend Security provides for both platforms and for both licensing models: Brotherhood Key Manager for AWS and Alliance Key Manager for Azure. Both the AWS and the Azure instances are dedicated key managers in an IaaS virtual instance and likewise savour the flexibility of existence the aforementioned key managing director that is deployed equally an HSM, Cloud HSM, and VMware instance so that your environment tin scale by AWS and Azure, if needed. This is useful for organizations with existing (or hereafter) physical data center(s), because having the same engineering secure your information everywhere reduces complexity for your IT staff every bit they utilize and maintain information technology. ^Back to Top A very simple internal PKI installation (as shown in the graphic would flow like this: As defined by NIST in, "Introduction to Public Key Engineering science and the Federal PKI Infrastructure", the PKI environment consists of: Below is a curated list of what Oasis further defines in Section 4 every bit what the key direction client can asking of the central direction server: For farther reading on KMIP, try the KMIP Usage Guide Version 1.ii, Edited by Indra Fitzgerald and Judith Furlong. ^Back to Top In Department iii.five of PCI DSS, organizations that process, store, or transmit cardholder data should, "certificate and implement procedures to protect keys used to secure stored cardholder data against disclosure and misuse." This includes: As well, Section three.half-dozen requires that you "fully document and implement all primal direction processes and procedures for cryptographic keys used for encryption of cardholder data." This includes securely: As a part of this mission the organization has published a document, "Security Guidance For Critical Areas of Focus In Cloud Calculating," to help vendors and customers accomplish more secure applications in deject environments. The published guidance is at present in its tertiary edition and is available from the organisation's web site. The guidance provides recommendations for encryption key management in the section "Domain 11 – Encryption and Cardinal Management". Hither are the three main points that the CSA stresses for encryption primal direction: Hither also is a curated listing of their requirements for encryption and central direction: Article 32 also calls for "the pseudonymisation and encryption of personal information." If an organization does then, Article 34 states that the strict information alienation disclosure laws of Article 33 will not be enforced if, The GDPR places a high priority on protecting information at rest with encryption. Since encryption key management is part of an overall encryption strategy, it should be considered part in bundle with complying with EU law. ^Back to Top Encryption has been effectually for millenniums. Some of the primeval mentions of information technology come from the Arthashastra, a treatise on Imperial Indian governance written c2nd century BCE. In it, it describes giving messages to state spies in "clandestine writing". Subsequently, and in arguably the well-nigh famous form of aboriginal encryption, Julius Caesar sent letters to his boxing front generals in code. Known as the Caesar Cipher, it is a: Unfortunately for Caesar, and fortunately for his opponents, in one case the aught is known, all messages tin can exist hands read. Thus rendering the cipher useless. There needed to be a meliorate way. Fast forward to the electronic historic period. In the 1921 Edward Hebern patented the Hebern Electric Super Code Cipher Machine. It was the first to code the message with a hugger-mugger fundamental embedded in a detachable rotor. In recently declassified documents, the NSA showed that the machine enciphered the message by having the operator type the message in and the ciphertext would announced in a lite-lath, one alphabetic character at a time. Just since the encryption key was express by the utilise of one rotor, consisting of 26 circuit points, it was ultimately cleaved past cryptanalysis, specifically letter of the alphabet frequencies. The existent leap forward was the Enigma Machine of Earth War Ii, developed past the Germans in the 1920s. It used three rotors and was idea unbreakable since the Germans, during the war, changed the rotors once a day, "giving 159 million 1000000 million possible settings to choose from," estimates Bletchley Park. But, the Enigma machine was compromised by the Poles in 1932 using mathematical techniques. Afterwards, this early work was used to read encrypted messages during World War II past, amidst others, Alan Turing (at Bletchley Park) and the use of the then latest data crunching computers. Sending messages securely had come a long way from simple substitution ciphers. Keys were now beingness used - but they could exist croaky using the brute forcefulness of the latest computers. Enter: Data Encryption Standard. Beginning published equally the FIPS 46 standard in 1977, in 1987 the US Government, nether the Calculator Security Act, mandated that the National Institute of Standards and Technology (NIST) consequence the Data Encryption Standard (DES) in which it "specifies 2 FIPS canonical cryptographic algorithms." It also mandated that the "DES key consists of 64 binary digits ("0"due south or "1"south) of which 56 bits are randomly generated and used directly by the algorithm. The other 8 bits, which are not used by the algorithm, may be used for error detection." DES was considered very secure at the time. But in piffling more a decade, and as computers became exponentially faster, DES keys rapidly became vulnerable to brute force attacks. Two options were proposed to address the consequence around the aforementioned fourth dimension. The start, introduced in 1997, was Triple Data Encryption Algorithm (TDEA) or as it is more than ordinarily know: Triple Data Encryption Standard (3DES). As NIST describes the cryptographic technique: Just 3DES, when using only 112 $.25, is still vulnerable to attacks such equally chosen-plaintext attacks. Besides, since 3DES is a multi-step encryption procedure using ii or iii encryption keys, a stronger, more efficient method was needed. In 1997 NIST started a process to identify a replacement for DES. NIST invited cryptography and data security specialists from around the world to participate in the word and option process. V encryption algorithms were adopted for report. Through a procedure of consensus the encryption algorithm proposed by the Belgian cryptographers Joan Daeman and Vincent Rijmen was selected. Prior to choice Daeman and Rijmen used the name Rijndael (derived from their names) for the algorithm. Subsequently adoption the encryption algorithm was given the proper noun Advanced Encryption Standard (AES) which is in mutual use today. In 2000 NIST formally adopted the AES encryption algorithm and published it as a federal standard under the designation FIPS-197. AES encryption uses a single primal as a part of the encryption process. The key can be 128 bits (16 bytes), 192 bits (24 bytes), or 256 bits (32 bytes) in length. Given that the fastest computer would take billions of years to run through every permutation of a 256-bit primal, AES is considered an extremely secure encryption standard. This brings usa to today. AES is a very sophisticated encryption standard with an encryption key and can withstand the onslaught of the fastest computers. It's only vulnerability? The encryption keys falling into the wrong hands. That is why, after you have deployed your encryption, your all-time line of defense is a robust encryption central management strategy. ![]()
![]()
![]()
![]()
What is Encryption Key Direction?
Shortcuts
Introduction
"The proper direction of cryptographic keys is essential to the effective use of cryptography for security. Keys are coordinating to the combination of a safe. If a safe combination is known to an adversary, the strongest safe provides no security against penetration. Similarly, poor key direction may easily compromise stiff algorithms."
~ NIST Recommendation for Key Management
NIST's argument paints an accurate pic. Similar a safety's combination, your encryption keys are but as skillful as the security you use to protect them. At that place is an entire physical and digital cryptosystem that must be must be deemed for every bit well every bit each key's full lifecycle. Therefore, a robust encryption key management organization and policies includes:
Types of Encryption Keys
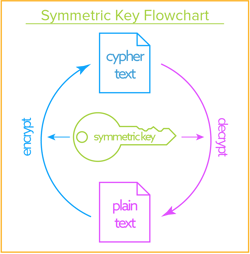
Symmetric Keys: Data-at-Rest
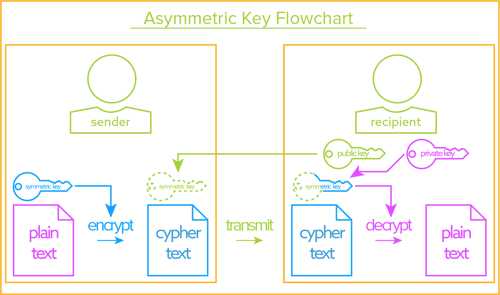
Asymmetric Keys: Data-in-Movement
How Encryption Cardinal Systems Piece of work
Symmetric Primal Systems
![]() This is an interactive graphic, click on the numbers above to larn more most each step
This is an interactive graphic, click on the numbers above to larn more most each step
Disproportionate Central Systems
The Full Life-Bike of Keys
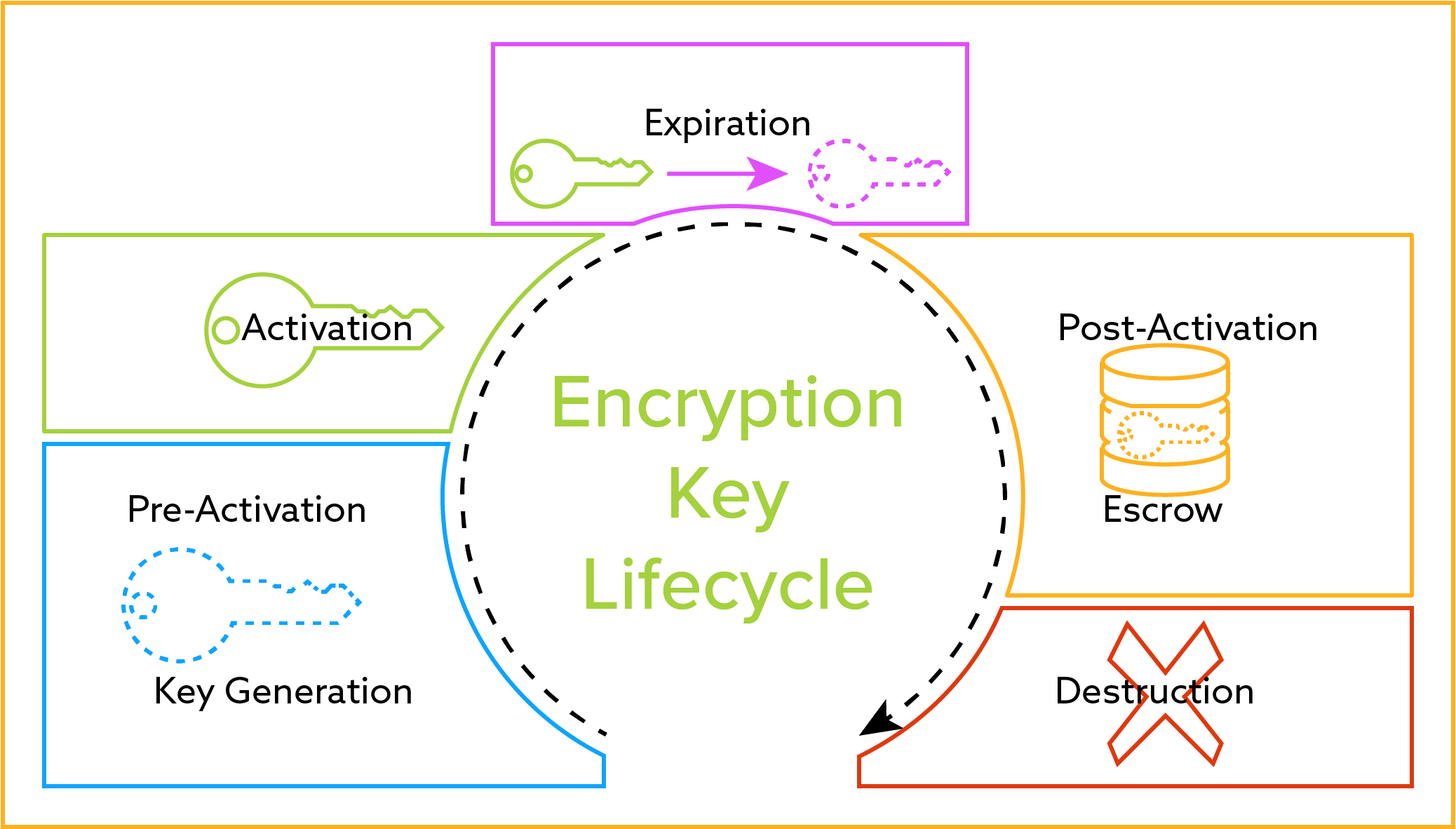
Cardinal Creation (Generation & Pre-Activation)
Cardinal Apply and Rollover (Activation through Post-Activation)
The key director should allow an activated cardinal to exist retrieved by authorized systems and users for encryption or decryption processes. It should likewise seamlessly manage current and by instances of the encryption fundamental. For example, if a new cardinal is generated and the old i deactivated (or rolled) every twelvemonth, then the primal director should retain previous versions of the cardinal merely manipulate only the current instance and actuate previous versions for decryption processes. Previous versions can still be retrieved in social club to decrypt data encrypted with such versions of the key. The key director volition also gyre the central either through a previously established schedule or allow an administrator to manually roll the key.Primal Revocation
Back Upwards (Escrow)
Key Deletion (Destruction)
Segregated Roles in Central Management
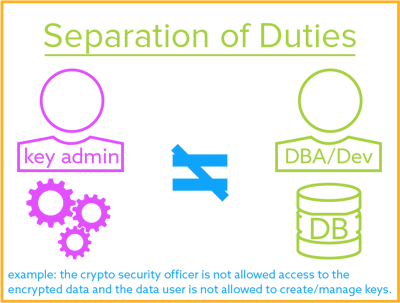
Separation of Duties
A security principle that divides critical functions amongst different staff members in an endeavour to ensure that no i individual has plenty data or admission privilege to perpetrate damaging fraud.
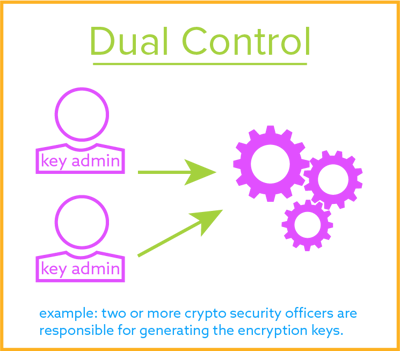
Dual Control
A process that uses 2 or more separate entities (unremarkably persons) operating in concert to protect sensitive functions or information. No single entity is able to access or use the materials, e.chiliad., cryptographic keys.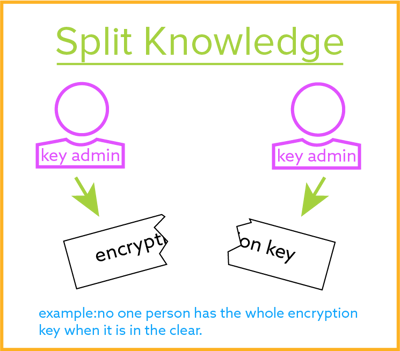
Split Knowledge
The Domains to Secure Encryption Keys
Physical Security
"Physical and ecology security controls" should be "implemented to protect the facility housing system resources, the system resource themselves, and the facilities used to support their performance."
How an Encryption Cardinal Manager is Validated
 Logical Admission Security
Logical Admission Security
User/Role Access
High Availability and Business Continuity
Platforms for Housing the Primal Manager
HSM
Hosted HSM
Virtual
 AWS, Microsoft Azure, and More: Dedicated or "as a Service"
AWS, Microsoft Azure, and More: Dedicated or "as a Service"Communication Protocols
PKI
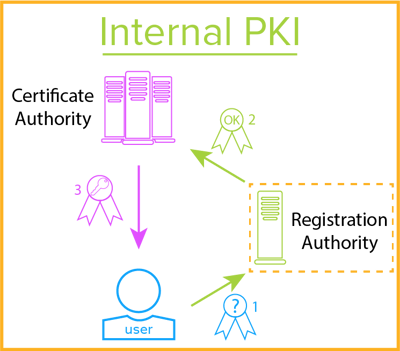 Public key infrastructure (PKI): NIST defines PKI as an infrastructure that "binds public keys to entities, enables other entities to verify public key bindings, and provides the services needed for ongoing management of keys in a distributed system." Put some other way, it is a cryptographic infrastructure consisting of the software, hardware, roles, procedures, and policies needed to properly manage and distribute public keys (such as a digital document) and private keys.
Public key infrastructure (PKI): NIST defines PKI as an infrastructure that "binds public keys to entities, enables other entities to verify public key bindings, and provides the services needed for ongoing management of keys in a distributed system." Put some other way, it is a cryptographic infrastructure consisting of the software, hardware, roles, procedures, and policies needed to properly manage and distribute public keys (such as a digital document) and private keys.
KMIP
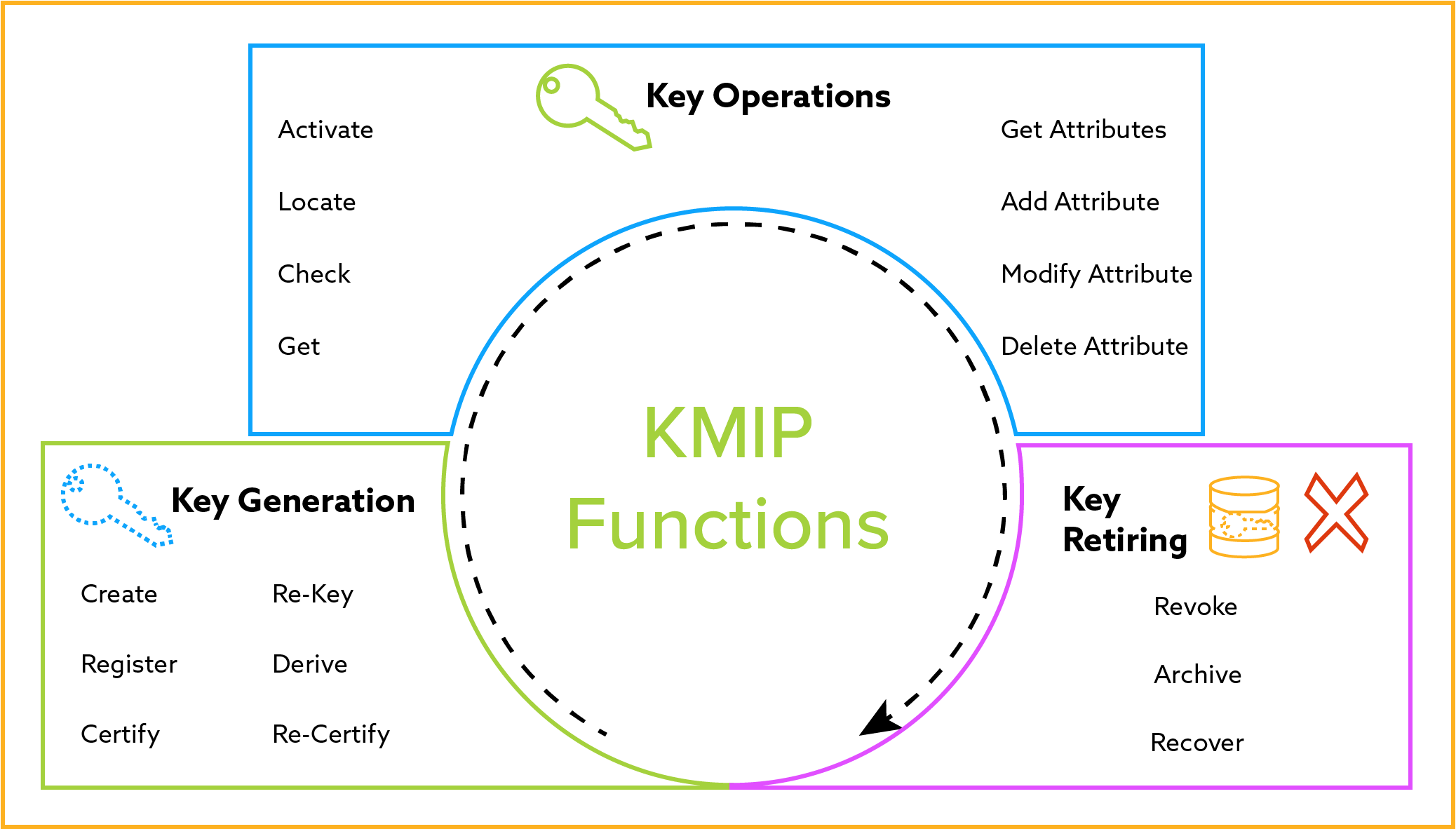 Key Direction Interoperability Protocol (KMIP): Every bit defined by OASIS, KMIP is a advice "protocol used for the communication between clients and servers to perform certain management operations on objects stored and maintained past a fundamental management system." This protocol is a standardized way of managing encryption keys throughout the lifecycle of the primal and is designed to facilitate "symmetric and disproportionate cryptographic keys, digital certificates, and templates used to simplify the creation of objects and control their use."
Key Direction Interoperability Protocol (KMIP): Every bit defined by OASIS, KMIP is a advice "protocol used for the communication between clients and servers to perform certain management operations on objects stored and maintained past a fundamental management system." This protocol is a standardized way of managing encryption keys throughout the lifecycle of the primal and is designed to facilitate "symmetric and disproportionate cryptographic keys, digital certificates, and templates used to simplify the creation of objects and control their use."
Encryption Key Management in Coming together Compliance
PCI DSS

 Payment carte du jour industry Data Security Standard (PCI DSS) is a widely accepted set of regulations intended to secure credit, debit and cash card transactions and cardholder data. PCI DSS requires that merchants protect sensitive cardholder information from loss and apply skillful security practices to find and protect against security breaches.
Payment carte du jour industry Data Security Standard (PCI DSS) is a widely accepted set of regulations intended to secure credit, debit and cash card transactions and cardholder data. PCI DSS requires that merchants protect sensitive cardholder information from loss and apply skillful security practices to find and protect against security breaches.
HIPAA HITECH
 The Health Insurance Portability and Accountability Act (HIPAA) and the Health Information technology for Economic and Clinical Health (HITECH) Human activity both seek greater adoption and meaningful use of wellness it. Both also lay out guidelines and regulations for proper data security around Electronic Protected Health Information (ePHI). Compliance with the HIPAA Security Rules and HIPAA Privacy Rules for ePHI requires the utilize of security technologies and best practices to demonstrate strong efforts towards complying with this federal regulation.
The Health Insurance Portability and Accountability Act (HIPAA) and the Health Information technology for Economic and Clinical Health (HITECH) Human activity both seek greater adoption and meaningful use of wellness it. Both also lay out guidelines and regulations for proper data security around Electronic Protected Health Information (ePHI). Compliance with the HIPAA Security Rules and HIPAA Privacy Rules for ePHI requires the utilize of security technologies and best practices to demonstrate strong efforts towards complying with this federal regulation.SOX
 The Sarbanes-Oxley (SOX) Human activity was passed to protect investors from the possibility of fraudulent accounting activities by corporations. The Sarbanes-Oxley Act (SOX) mandated strict reforms to improve fiscal disclosures from corporations and preclude accounting fraud. Sections 302, 304, and 404 of the Sarbanes-Oxley Human action mandate that organizations build, maintain, and annually report on the data security and internal controls used safeguard their sensitive data from misuse and fraud.
The Sarbanes-Oxley (SOX) Human activity was passed to protect investors from the possibility of fraudulent accounting activities by corporations. The Sarbanes-Oxley Act (SOX) mandated strict reforms to improve fiscal disclosures from corporations and preclude accounting fraud. Sections 302, 304, and 404 of the Sarbanes-Oxley Human action mandate that organizations build, maintain, and annually report on the data security and internal controls used safeguard their sensitive data from misuse and fraud.Cloud Security Alliance
 While the Cloud Security Brotherhood is not a governmental agency able to levy fines for non-compliance of their standards, it is an non-for-profit organization of cloud vendors, users, and security experts whose mission is "To promote the utilise of best practices for providing security assurance within Cloud Computing, and provide teaching on the uses of Deject Calculating to help secure all other forms of computing." They currently have over 80,000 members and growing. So befitting to their standards is in the best interest of many companies worldwide.
While the Cloud Security Brotherhood is not a governmental agency able to levy fines for non-compliance of their standards, it is an non-for-profit organization of cloud vendors, users, and security experts whose mission is "To promote the utilise of best practices for providing security assurance within Cloud Computing, and provide teaching on the uses of Deject Calculating to help secure all other forms of computing." They currently have over 80,000 members and growing. So befitting to their standards is in the best interest of many companies worldwide.Domain xi - Encryption & Fundamental Management
EU GDPR
 The new European Union Full general Data Protection Regulation (European union GDPR) has now passed both the EU Council and Parliament and replaces the earlier Data Protection Directive (Directive 94/46/EC). In Provision 83 it states:
The new European Union Full general Data Protection Regulation (European union GDPR) has now passed both the EU Council and Parliament and replaces the earlier Data Protection Directive (Directive 94/46/EC). In Provision 83 it states: In order to maintain security and to forestall processing in infringement of this Regulation, the controller or processor should evaluate the risks inherent in the processing and implement measures to mitigate those risks, such as encryption.
the controller has implemented advisable technical and organisational protection measures, and those measures were practical to the personal data afflicted by the personal information breach, in particular those that render the personal information unintelligible to whatever person who is not authorised to access it, such as encryption.
CAP 486
 Hong Kong's CAP 486 Personal Information (Privacy) Ordinance requires that all practical steps will exist taken to ensure that personally identifiable information, held past a information user, are protected confronting unauthorized or accidental access. Such considerations should be the kind of data stored and the damage that could result if any of those things should occur; the physical location where the information is stored; and any security measures incorporated into any equipment in which the data is stored.
Hong Kong's CAP 486 Personal Information (Privacy) Ordinance requires that all practical steps will exist taken to ensure that personally identifiable information, held past a information user, are protected confronting unauthorized or accidental access. Such considerations should be the kind of data stored and the damage that could result if any of those things should occur; the physical location where the information is stored; and any security measures incorporated into any equipment in which the data is stored.APPI
 Japan's Act on the Protection of Personal Information contains policies that are guidelines, merely not laws, governing the protection of personal information. Information technology requires that businesses handling personal information should take all necessary and proper measures for the prevention of leakage, loss, or impairment.
Japan's Act on the Protection of Personal Information contains policies that are guidelines, merely not laws, governing the protection of personal information. Information technology requires that businesses handling personal information should take all necessary and proper measures for the prevention of leakage, loss, or impairment.PA 1988 & PA 2000
 Commonwealth of australia's Privacy Act of 1988 and the Privacy Amendment Act of 2000 govern data security for the Down Nether. In information technology, businesses must accept all reasonable steps to protect personally identifiable data in its databases from abuse or theft. An system must also destroy or permanently de‑identify personal information if it is no longer needed.
Commonwealth of australia's Privacy Act of 1988 and the Privacy Amendment Act of 2000 govern data security for the Down Nether. In information technology, businesses must accept all reasonable steps to protect personally identifiable data in its databases from abuse or theft. An system must also destroy or permanently de‑identify personal information if it is no longer needed. Bonus Content
A Brief History - the Need for Encryption Central Management
"substitution goose egg in which each letter in the plaintext is 'shifted' a certain number of places down the alphabet. For example, with a shift of 1, A would be replaced by B, B would become C, and so on."
[3DES] encrypts each block iii times with the DES algorithm, using either ii or 3 unlike 56-bit keys. This approach yields effective key lengths of 112 or 168 bits

![]()
![]()
![]()
![]()
holbrookthavatabot1971.blogspot.com
Source: https://info.townsendsecurity.com/definitive-guide-to-encryption-key-management-fundamentals
Post a Comment for "what to do with an encrypted cache key"